444 Alaska Avenue
Suite #BAA205 Torrance, CA 90503 USA
+1 424 999 9627
24/7 Customer Support
sales@markwideresearch.com
Email us at
Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at
Corporate User License
Unlimited User Access, Post-Sale Support, Free Updates, Reports in English & Major Languages, and more
$2450
Market Overview
The US hardware encryption market is a crucial segment within the broader cybersecurity industry, focusing on the development and deployment of encryption solutions for data protection. Hardware encryption involves the use of dedicated cryptographic hardware devices to secure sensitive data, offering enhanced security and performance compared to software-based encryption methods. With increasing cyber threats and data breaches, the demand for robust encryption solutions has grown, driving the expansion of the hardware encryption market in the US.
Meaning
Hardware encryption refers to the process of encrypting data using dedicated cryptographic hardware devices, such as encryption chips, modules, or drives, to safeguard information from unauthorized access or interception. Unlike software-based encryption, which relies on computer resources for encryption and decryption processes, hardware encryption offloads cryptographic operations to specialized hardware components, providing stronger protection against cyber threats and ensuring faster data processing speeds.
Executive Summary
The US hardware encryption market has experienced significant growth in recent years, fueled by escalating cybersecurity concerns, stringent regulatory requirements, and increasing adoption of data encryption solutions across various industries. As organizations strive to protect their sensitive data from cyberattacks and data breaches, hardware encryption solutions have emerged as a preferred choice for achieving robust security, compliance, and performance requirements.

Important Note: The companies listed in the image above are for reference only. The final study will cover 18–20 key players in this market, and the list can be adjusted based on our client’s requirements.
Key Market Insights
Market Drivers
Market Restraints
Market Opportunities
Market Dynamics
The US hardware encryption market operates in a dynamic environment shaped by technological advancements, regulatory developments, evolving threat landscapes, and changing customer preferences. Market dynamics such as mergers and acquisitions, partnerships and collaborations, product innovations, and competitive strategies influence the growth and competitiveness of hardware encryption vendors in the US market.
Regional Analysis
The US hardware encryption market is characterized by strong demand from various industries, including finance, healthcare, government, defense, and IT, driving market growth across different regions and states. Key technology hubs such as Silicon Valley, Boston, and Seattle serve as centers of innovation and investment in hardware encryption technologies, fostering industry collaboration and talent development.
Competitive Landscape
Leading Companies in the US Hardware Encryption Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
Segmentation
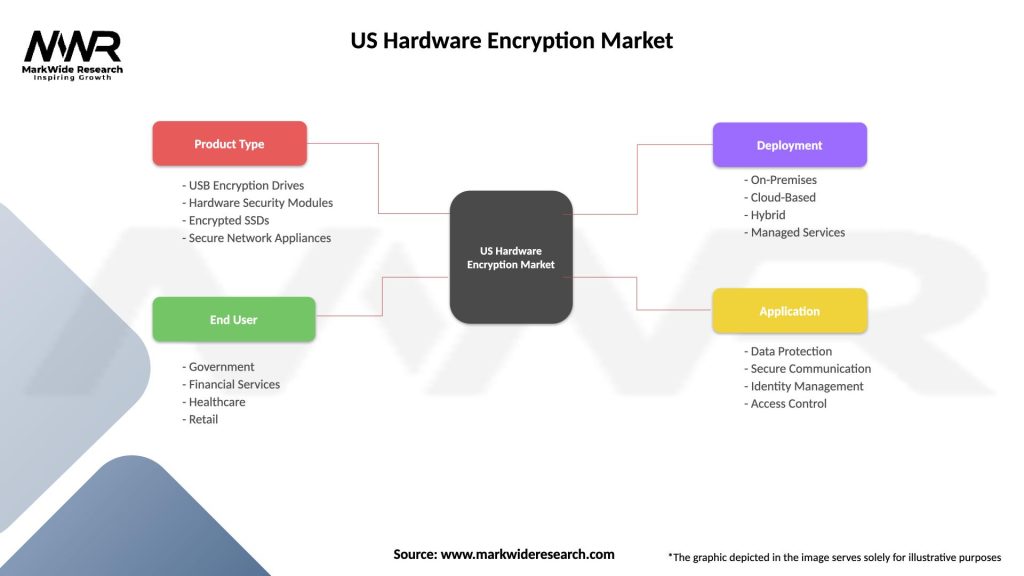
The US hardware encryption market can be segmented based on various factors such as product type, application, end-user industry, and geography. Common segmentation categories include:
Segmentation enables vendors and stakeholders to identify target markets, tailor their product offerings, and develop targeted marketing strategies to address specific customer needs and industry verticals.
Category-wise Insights
Key Benefits for Industry Participants and Stakeholders
SWOT Analysis
A SWOT analysis provides insights into the strengths, weaknesses, opportunities, and threats facing the US hardware encryption market:
Understanding these factors enables stakeholders to capitalize on market opportunities, address weaknesses, mitigate threats, and leverage strengths to maintain a competitive edge in the US hardware encryption market.
Market Key Trends
Covid-19 Impact
The COVID-19 pandemic has accelerated the adoption of hardware encryption solutions as organizations prioritize data security and privacy in remote work environments. With the rapid shift to remote work, cloud-based collaboration, and digital transformation initiatives, the need for secure encryption technologies to protect sensitive data has become paramount, driving market demand for hardware encryption solutions.
Key Industry Developments
Analyst Suggestions
Future Outlook
The US hardware encryption market is poised for continued growth and innovation, driven by escalating cybersecurity threats, increasing regulatory pressures, and growing adoption of encryption solutions across diverse industries. Opportunities for market expansion abound as organizations prioritize data security, privacy, and compliance, fueling demand for hardware encryption solutions that offer robust protection, performance, and scalability. However, challenges such as cost considerations, integration complexity, and evolving threat landscapes need to be addressed to unlock the full potential of hardware encryption technologies in safeguarding sensitive data and digital assets.
Conclusion
The US hardware encryption market plays a critical role in addressing cybersecurity challenges and protecting sensitive data from unauthorized access, data breaches, and cyber threats. With increasing reliance on digital technologies, cloud services, and IoT devices, the demand for robust encryption solutions continues to rise, driving market growth and innovation in hardware-based encryption technologies. By investing in quantum-safe encryption, adopting zero trust security frameworks, enhancing endpoint security, and leveraging hardware security modules (HSMs), organizations can strengthen their data protection strategies, mitigate risks, and ensure compliance with regulatory requirements in an increasingly interconnected and digitalized world.
What is Hardware Encryption?
Hardware encryption refers to the process of encrypting data using dedicated hardware devices, which provide enhanced security and performance compared to software-based solutions. This technology is commonly used in various applications, including secure data storage, communication, and device authentication.
What are the key players in the US Hardware Encryption Market?
Key players in the US Hardware Encryption Market include companies like Thales, Gemalto, and IBM, which offer a range of hardware encryption solutions for data protection and secure communications. These companies are known for their innovative technologies and extensive product portfolios, among others.
What are the growth factors driving the US Hardware Encryption Market?
The US Hardware Encryption Market is driven by increasing concerns over data security, the rise in cyber threats, and the growing adoption of cloud services. Additionally, regulatory compliance requirements for data protection are pushing organizations to invest in hardware encryption solutions.
What challenges does the US Hardware Encryption Market face?
Challenges in the US Hardware Encryption Market include the high cost of implementation and the complexity of integrating hardware encryption solutions into existing systems. Furthermore, the rapid pace of technological advancements can make it difficult for companies to keep up with the latest security measures.
What opportunities exist in the US Hardware Encryption Market?
The US Hardware Encryption Market presents opportunities for growth through advancements in encryption technologies and the increasing demand for secure mobile devices. Additionally, the expansion of IoT devices and the need for secure data transmission in various industries are likely to drive market growth.
What trends are shaping the US Hardware Encryption Market?
Trends in the US Hardware Encryption Market include the integration of artificial intelligence for enhanced security measures and the development of more compact and efficient encryption hardware. Moreover, the shift towards remote work and cloud computing is increasing the demand for robust hardware encryption solutions.
US Hardware Encryption Market
| Segmentation Details | Description |
|---|---|
| Product Type | USB Encryption Drives, Hardware Security Modules, Encrypted SSDs, Secure Network Appliances |
| End User | Government, Financial Services, Healthcare, Retail |
| Deployment | On-Premises, Cloud-Based, Hybrid, Managed Services |
| Application | Data Protection, Secure Communication, Identity Management, Access Control |
Please note: The segmentation can be entirely customized to align with our client’s needs.
Leading Companies in the US Hardware Encryption Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
Trusted by Global Leaders
Fortune 500 companies, SMEs, and top institutions rely on MWR’s insights to make informed decisions and drive growth.
ISO & IAF Certified
Our certifications reflect a commitment to accuracy, reliability, and high-quality market intelligence trusted worldwide.
Customized Insights
Every report is tailored to your business, offering actionable recommendations to boost growth and competitiveness.
Multi-Language Support
Final reports are delivered in English and major global languages including French, German, Spanish, Italian, Portuguese, Chinese, Japanese, Korean, Arabic, Russian, and more.
Unlimited User Access
Corporate License offers unrestricted access for your entire organization at no extra cost.
Free Company Inclusion
We add 3–4 extra companies of your choice for more relevant competitive analysis — free of charge.
Post-Sale Assistance
Dedicated account managers provide unlimited support, handling queries and customization even after delivery.
GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at