444 Alaska Avenue
Suite #BAA205 Torrance, CA 90503 USA
+1 424 999 9627
24/7 Customer Support
sales@markwideresearch.com
Email us at
Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at
Corporate User License
Unlimited User Access, Post-Sale Support, Free Updates, Reports in English & Major Languages, and more
$3450
Market Overview
The Threat Hunting market is witnessing significant growth in recent years due to the increasing frequency and complexity of cyber threats. Threat hunting refers to the proactive approach of identifying and mitigating potential cyber threats by actively searching for indicators of compromise within an organization’s network. It involves a combination of manual and automated techniques to detect and respond to advanced persistent threats (APTs) and other sophisticated attacks.
Meaning
Threat hunting is a cybersecurity practice that aims to identify and eliminate threats that have bypassed traditional security measures, such as firewalls and antivirus software. It goes beyond reactive incident response and focuses on actively searching for signs of malicious activities within an organization’s network. By taking a proactive approach, threat hunting enables organizations to detect and neutralize threats before they can cause significant damage.
Executive Summary
The Threat Hunting market is experiencing rapid growth, driven by the escalating cyber threats faced by organizations worldwide. The increasing number of data breaches and cyber attacks has highlighted the need for proactive security measures. Threat hunting offers a proactive and effective solution to identify and neutralize threats that have evaded traditional security controls. As a result, organizations are investing in threat hunting tools and services to enhance their cybersecurity posture and protect sensitive data.
Important Note: The companies listed in the image above are for reference only. The final study will cover 18–20 key players in this market, and the list can be adjusted based on our client’s requirements.
Key Market Insights
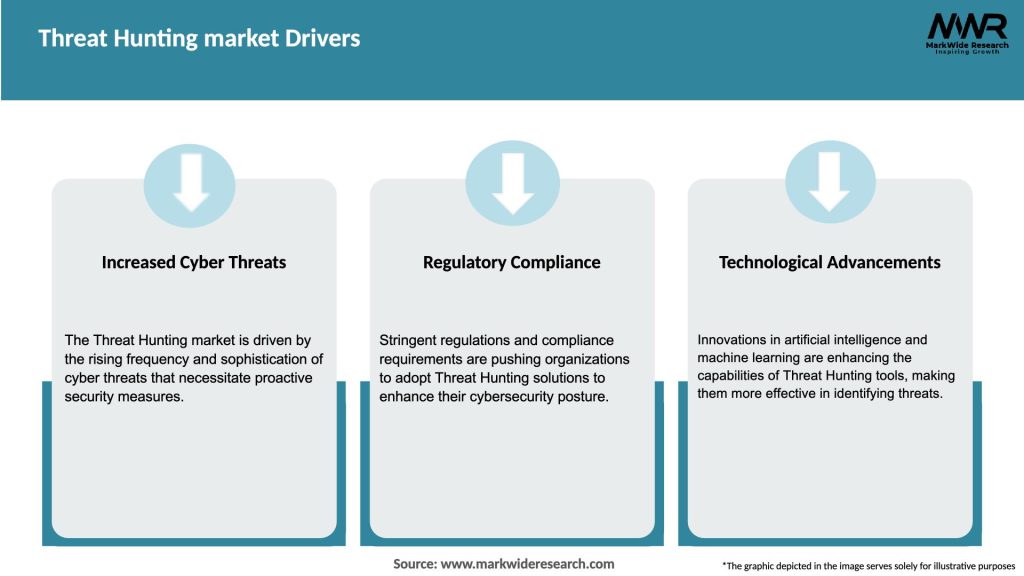
Market Drivers
Market Restraints
Market Opportunities

Market Dynamics
The Threat Hunting market is driven by the increasing frequency and complexity of cyber threats. Organizations are recognizing the limitations of traditional security measures and are shifting towards proactive threat hunting practices. The market is highly competitive, with numerous vendors offering a range of threat hunting solutions and services. To stay competitive, vendors are focusing on developing advanced analytics capabilities, integrating AI and ML technologies, and expanding their service offerings.
Regional Analysis
The Threat Hunting market is witnessing significant growth across all major regions, including North America, Europe, Asia Pacific, Latin America, and the Middle East and Africa. North America holds the largest market share, driven by the presence of major cybersecurity vendors, high cybersecurity spending, and strict data protection regulations. Europe is also a prominent market, with stringent regulatory frameworks and a growing emphasis on data privacy. The Asia Pacific region is experiencing rapid growth due to the increasing adoption of digital technologies and rising cyber threats.
Competitive Landscape
Leading Companies in Threat Hunting Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
Segmentation
The Threat Hunting market can be segmented based on the following criteria:
Category-wise Insights
Key Benefits for Industry Participants and Stakeholders
SWOT Analysis
The Threat Hunting market can be analyzed using the following SWOT framework:
Market Key Trends
Covid-19 Impact
The COVID-19 pandemic has had a significant impact on the Threat Hunting market. The sudden shift to remote work and the increased reliance on digital infrastructure created new opportunities for cybercriminals. The surge in cyber attacks during the pandemic has highlighted the importance of proactive threat hunting practices. Organizations across industries have accelerated their investments in threat hunting solutions to protect their remote workforce and secure their digital assets.
Key Industry Developments
Analyst Suggestions
Future Outlook
The future of the Threat Hunting market looks promising, with sustained growth expected in the coming years. The increasing sophistication of cyber threats, coupled with the growing adoption of digital technologies, will drive the demand for proactive threat hunting solutions. Vendors will continue to invest in advanced analytics, AI, and ML technologies to enhance threat detection capabilities. The market will also witness increased collaboration and partnerships between threat hunting solution providers and other cybersecurity vendors. As organizations prioritize proactive security measures, threat hunting will become an integral part of their cybersecurity strategies.
Conclusion
The Threat Hunting market is witnessing significant growth as organizations recognize the need for proactive cybersecurity measures. Threat hunting offers a proactive approach to identifying and mitigating potential cyber threats, enabling organizations to detect and respond to advanced attacks that have evaded traditional security measures. While there are challenges such as the skill gap and high implementation costs, the market presents ample opportunities for vendors to develop advanced threat hunting solutions and cater to the evolving needs of organizations. As the cyber threat landscape continues to evolve, threat hunting will play a crucial role in safeguarding organizations’ digital assets and maintaining data security.
What is Threat Hunting?
Threat hunting is a proactive cybersecurity practice that involves searching for signs of malicious activities within an organization’s network. It aims to identify and mitigate threats before they can cause significant damage.
What are the key players in the Threat Hunting market?
Key players in the Threat Hunting market include CrowdStrike, FireEye, and Palo Alto Networks, which provide advanced threat detection and response solutions. These companies focus on enhancing security through innovative technologies and threat intelligence, among others.
What are the main drivers of growth in the Threat Hunting market?
The growth of the Threat Hunting market is driven by the increasing frequency of cyberattacks, the need for advanced security measures, and the rising adoption of cloud-based solutions. Organizations are prioritizing proactive threat detection to safeguard sensitive data.
What challenges does the Threat Hunting market face?
The Threat Hunting market faces challenges such as a shortage of skilled cybersecurity professionals and the complexity of integrating threat hunting tools with existing security infrastructures. Additionally, evolving cyber threats require continuous adaptation and investment.
What opportunities exist in the Threat Hunting market?
Opportunities in the Threat Hunting market include the development of AI-driven threat detection tools and the expansion of managed security services. As organizations increasingly recognize the importance of proactive security, demand for innovative solutions is expected to grow.
What trends are shaping the Threat Hunting market?
Trends in the Threat Hunting market include the integration of machine learning for enhanced threat detection and the rise of automated threat hunting solutions. Additionally, there is a growing emphasis on collaboration between security teams and threat intelligence sharing.
Threat Hunting market
| Segmentation Details | Description |
|---|---|
| Deployment | On-Premises, Cloud-Based, Hybrid, Managed Services |
| End User | Government, BFSI, Healthcare, Retail |
| Solution | Threat Intelligence, Incident Response, Vulnerability Management, Security Information and Event Management |
| Technology | Machine Learning, Behavioral Analytics, Automation, Forensics |
Please note: The segmentation can be entirely customized to align with our client’s needs.
Leading Companies in Threat Hunting Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
North America
o US
o Canada
o Mexico
Europe
o Germany
o Italy
o France
o UK
o Spain
o Denmark
o Sweden
o Austria
o Belgium
o Finland
o Turkey
o Poland
o Russia
o Greece
o Switzerland
o Netherlands
o Norway
o Portugal
o Rest of Europe
Asia Pacific
o China
o Japan
o India
o South Korea
o Indonesia
o Malaysia
o Kazakhstan
o Taiwan
o Vietnam
o Thailand
o Philippines
o Singapore
o Australia
o New Zealand
o Rest of Asia Pacific
South America
o Brazil
o Argentina
o Colombia
o Chile
o Peru
o Rest of South America
The Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Israel
o Kuwait
o Oman
o North Africa
o West Africa
o Rest of MEA
Trusted by Global Leaders
Fortune 500 companies, SMEs, and top institutions rely on MWR’s insights to make informed decisions and drive growth.
ISO & IAF Certified
Our certifications reflect a commitment to accuracy, reliability, and high-quality market intelligence trusted worldwide.
Customized Insights
Every report is tailored to your business, offering actionable recommendations to boost growth and competitiveness.
Multi-Language Support
Final reports are delivered in English and major global languages including French, German, Spanish, Italian, Portuguese, Chinese, Japanese, Korean, Arabic, Russian, and more.
Unlimited User Access
Corporate License offers unrestricted access for your entire organization at no extra cost.
Free Company Inclusion
We add 3–4 extra companies of your choice for more relevant competitive analysis — free of charge.
Post-Sale Assistance
Dedicated account managers provide unlimited support, handling queries and customization even after delivery.
GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at