444 Alaska Avenue
Suite #BAA205 Torrance, CA 90503 USA
+1 424 999 9627
24/7 Customer Support
sales@markwideresearch.com
Email us at
Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at
Corporate User License
Unlimited User Access, Post-Sale Support, Free Updates, Reports in English & Major Languages, and more
$3450
Market Overview
The Insider Threat Protection market is a rapidly evolving sector in the cybersecurity industry, aiming to safeguard organizations from internal threats posed by employees, contractors, or business associates. Insider threats refer to the potential risks and vulnerabilities that arise from individuals with authorized access to an organization’s sensitive data, systems, or facilities. These threats can result in data breaches, intellectual property theft, financial losses, and reputational damage. As businesses increasingly digitize their operations, the need for robust insider threat protection solutions becomes paramount.
Meaning
Insider Threat Protection is a comprehensive approach that involves the implementation of various security measures, technologies, and policies to detect, prevent, and mitigate insider threats. It combines elements of user behavior analytics, data loss prevention, access controls, and identity and access management to create a multi-layered defense against potential malicious activities from within an organization.
Executive Summary
The Insider Threat Protection market has experienced substantial growth over the past few years, driven by the rising frequency and sophistication of insider threats. High-profile incidents of insider breaches have compelled organizations across industries to invest significantly in advanced security solutions. This market’s growth is expected to continue at a robust pace as businesses recognize the criticality of safeguarding their digital assets and intellectual property.
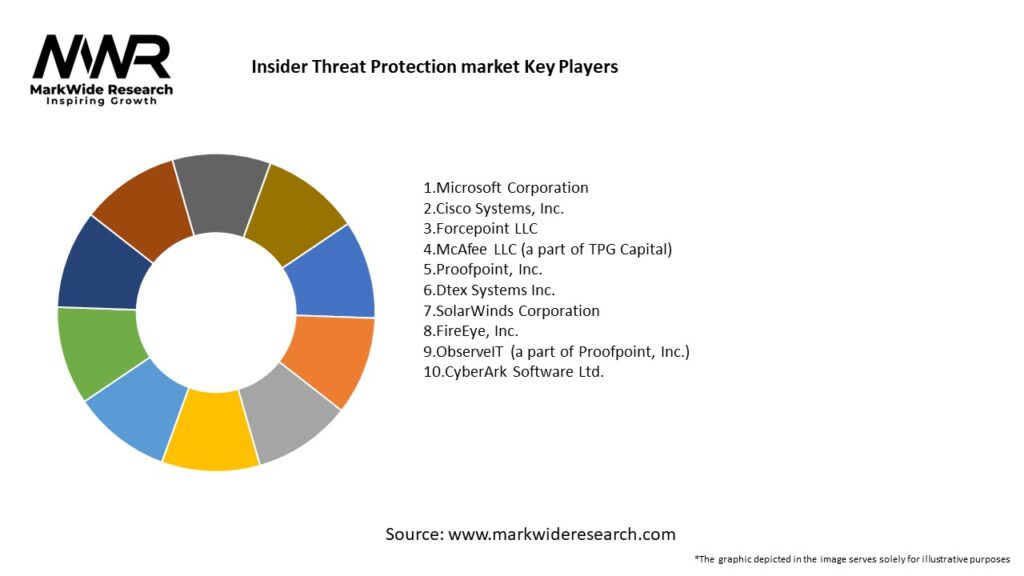
Important Note: The companies listed in the image above are for reference only. The final study will cover 18–20 key players in this market, and the list can be adjusted based on our client’s requirements.
Key Market Insights
Market Drivers
Market Restraints
Market Opportunities
Market Dynamics
The Insider Threat Protection market is characterized by dynamic and evolving factors that influence its growth. The increasing sophistication of insider threats, the adoption of cloud-based systems, and regulatory compliance drive market expansion. However, challenges related to integration, budget constraints, and privacy concerns may impede growth to some extent. The market offers substantial opportunities for technological advancements and SME adoption, and collaborative insider threat programs are set to shape its future landscape.
Regional Analysis
The Insider Threat Protection market exhibits a global presence, with North America holding the largest market share. The region’s dominance is attributed to its early adoption of cybersecurity technologies, presence of leading market players, and stringent data protection regulations. Europe and the Asia-Pacific region are also significant markets, driven by increasing cyber threats and regulatory focus on data security. Latin America and the Middle East and Africa are emerging markets with untapped potential, presenting growth opportunities for market players.
Competitive Landscape
Leading Companies in the Insider Threat Protection Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
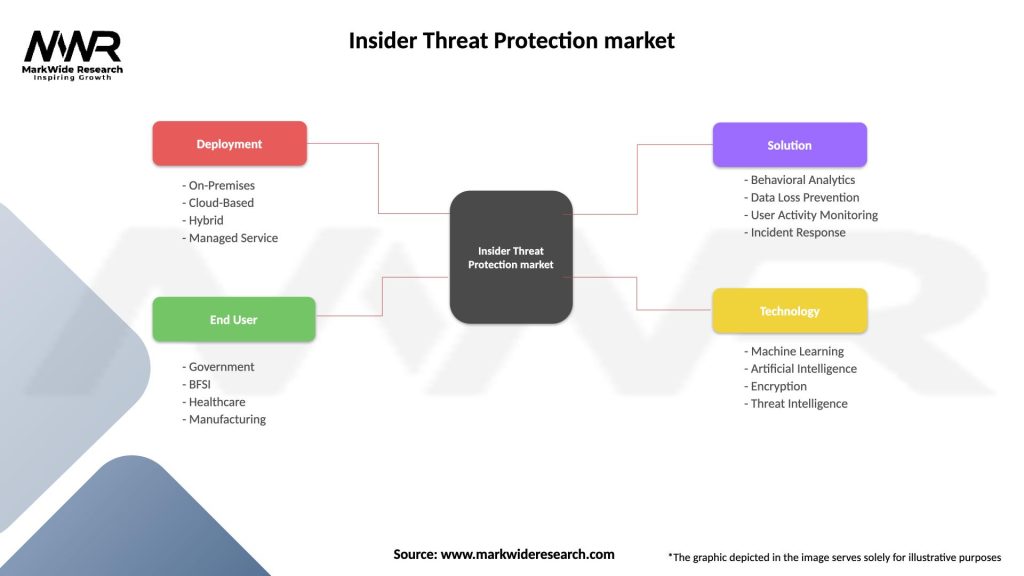
Segmentation
The Insider Threat Protection market can be segmented based on various factors, including:
Category-wise Insights
Key Benefits for Industry Participants and Stakeholders
SWOT Analysis
Strengths:
Weaknesses:
Opportunities:
Threats:
Market Key Trends
Covid-19 Impact
The COVID-19 pandemic has significantly impacted the Insider Threat Protection market. The rapid shift to remote work has increased the potential attack surface for insider threats. Organizations faced challenges in monitoring employee activities and ensuring data security outside traditional office setups. Consequently, there was an increased emphasis on the adoption of cloud-based solutions and user behavior analytics to detect and prevent insider threats. The pandemic has accelerated digital transformation initiatives, making insider threat protection a critical investment for businesses worldwide.
Key Industry Developments
Analyst Suggestions
Future Outlook
The Insider Threat Protection market is poised for substantial growth in the coming years. The increasing adoption of cloud-based services, advancements in AI and ML technologies, and the evolving threat landscape will shape the market’s future. Additionally, the implementation of stringent data protection regulations and the growing awareness of insider threats will further fuel market expansion.
Conclusion
The Insider Threat Protection market is witnessing rapid growth as organizations across industries recognize the importance of protecting their sensitive data and intellectual property from insider threats. The market offers a diverse range of solutions, including user behavior analytics, data loss prevention, and identity and access management, to safeguard against insider risks. Despite challenges related to integration and budget constraints, the market’s future outlook remains promising, driven by emerging technologies, collaborative programs, and regulatory compliance needs. The ongoing COVID-19 pandemic has accelerated the adoption of insider threat protection measures, making it a critical investment for businesses adapting to remote work and digital transformation initiatives. Organizations that prioritize insider threat protection will be better positioned to withstand evolving cybersecurity challenges and safeguard their assets and reputation.
What is Insider Threat Protection?
Insider Threat Protection refers to the strategies and technologies used to detect and mitigate risks posed by individuals within an organization who may misuse their access to sensitive information. This includes monitoring user behavior, implementing access controls, and conducting regular security training.
What are the key players in the Insider Threat Protection market?
Key players in the Insider Threat Protection market include companies like Proofpoint, Teramind, and Forcepoint, which provide solutions for monitoring and managing insider threats. These companies focus on various aspects such as data loss prevention, user activity monitoring, and behavioral analytics, among others.
What are the main drivers of growth in the Insider Threat Protection market?
The growth of the Insider Threat Protection market is driven by increasing incidents of data breaches, the rise of remote work, and the need for compliance with data protection regulations. Organizations are investing in these solutions to safeguard sensitive information and maintain trust with customers.
What challenges does the Insider Threat Protection market face?
The Insider Threat Protection market faces challenges such as the difficulty in accurately identifying insider threats without infringing on employee privacy and the potential for false positives. Additionally, the rapid evolution of technology can make it hard for organizations to keep their security measures up to date.
What opportunities exist in the Insider Threat Protection market?
Opportunities in the Insider Threat Protection market include the development of advanced analytics and machine learning technologies to enhance threat detection capabilities. Furthermore, as organizations increasingly adopt cloud services, there is a growing need for tailored solutions that address cloud-specific insider threats.
What trends are shaping the Insider Threat Protection market?
Trends in the Insider Threat Protection market include the integration of artificial intelligence for predictive analytics and the growing emphasis on employee training programs to foster a security-aware culture. Additionally, there is a shift towards more comprehensive security frameworks that encompass both insider and external threats.
Insider Threat Protection market
| Segmentation Details | Description |
|---|---|
| Deployment | On-Premises, Cloud-Based, Hybrid, Managed Service |
| End User | Government, BFSI, Healthcare, Manufacturing |
| Solution | Behavioral Analytics, Data Loss Prevention, User Activity Monitoring, Incident Response |
| Technology | Machine Learning, Artificial Intelligence, Encryption, Threat Intelligence |
Please note: The segmentation can be entirely customized to align with our client’s needs.
Leading Companies in the Insider Threat Protection Market:
Please note: This is a preliminary list; the final study will feature 18–20 leading companies in this market. The selection of companies in the final report can be customized based on our client’s specific requirements.
North America
o US
o Canada
o Mexico
Europe
o Germany
o Italy
o France
o UK
o Spain
o Denmark
o Sweden
o Austria
o Belgium
o Finland
o Turkey
o Poland
o Russia
o Greece
o Switzerland
o Netherlands
o Norway
o Portugal
o Rest of Europe
Asia Pacific
o China
o Japan
o India
o South Korea
o Indonesia
o Malaysia
o Kazakhstan
o Taiwan
o Vietnam
o Thailand
o Philippines
o Singapore
o Australia
o New Zealand
o Rest of Asia Pacific
South America
o Brazil
o Argentina
o Colombia
o Chile
o Peru
o Rest of South America
The Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Israel
o Kuwait
o Oman
o North Africa
o West Africa
o Rest of MEA
Trusted by Global Leaders
Fortune 500 companies, SMEs, and top institutions rely on MWR’s insights to make informed decisions and drive growth.
ISO & IAF Certified
Our certifications reflect a commitment to accuracy, reliability, and high-quality market intelligence trusted worldwide.
Customized Insights
Every report is tailored to your business, offering actionable recommendations to boost growth and competitiveness.
Multi-Language Support
Final reports are delivered in English and major global languages including French, German, Spanish, Italian, Portuguese, Chinese, Japanese, Korean, Arabic, Russian, and more.
Unlimited User Access
Corporate License offers unrestricted access for your entire organization at no extra cost.
Free Company Inclusion
We add 3–4 extra companies of your choice for more relevant competitive analysis — free of charge.
Post-Sale Assistance
Dedicated account managers provide unlimited support, handling queries and customization even after delivery.
GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


GET A FREE SAMPLE REPORT
This free sample study provides a complete overview of the report, including executive summary, market segments, competitive analysis, country level analysis and more.
ISO AND IAF CERTIFIED


Suite #BAA205 Torrance, CA 90503 USA
24/7 Customer Support
Email us at